Hotel Key Card Systems
Hotel Key Card Systems
Disclaimer
I am a software developer, not a cybersecurity professional, and this is my own personal exploration into a specific hotel’s security system - without insider knowledge. My understanding could be incorrect.
Additionally, exploiting systems in this manner is both illegal and harmful to real people. This is morally deplorable and I do not advise it.
Introduction
Why This Matters
I recently stayed at a hotel with my family where they gave us all bracelets with RFID chips. These bracelets could open our door and even charge purchases to our room at various hotel restaurants! However, the bracelets were (supposedly) useless until our room was ready, at which point I received a text message with our room number and our bracelets became functional.
I also noticed that the same bracelets were used by employees to access employee-only areas. Being inherently curious, I set out to understand - more or less - how the system worked (and how it didn’t work).
System Overview
Modern hotel key card systems integrate access control, payment systems, and guest management into a single platform. These systems must balance security, convenience, and operational efficiency - often leading to interesting compromises in implementation.
System Components
Physical Components
- Room Assignment: Your room number serves as a unique identifier in the system, linked to your personal details (email, phone, billing) in the Property Management System (PMS)
- Key Card/Bracelet (RFID)
- Key Encoder: The hardware device that writes encrypted access credentials to RFID cards/bracelets
- Key Card Readers: The endpoints of the system, mounted on doors and payment terminals
Software Systems
- Property Management System (PMS): The central database and management software that handles reservations, guest information, billing, and access control
- Front Desk Computer: The terminal that interfaces with both the PMS and key encoder
- Door Lock Software: Embedded systems that validate credentials and control access
Human Elements
- Front Desk Worker: Tired and stressed people who will give you anything to please just go away
- Guests: Also tired and stressed people, but for different reasons
- Hotel Staff: ALl the little worker bees with elevated access privileges for maintenance and operations
Technical Implementation
Access Control Flow
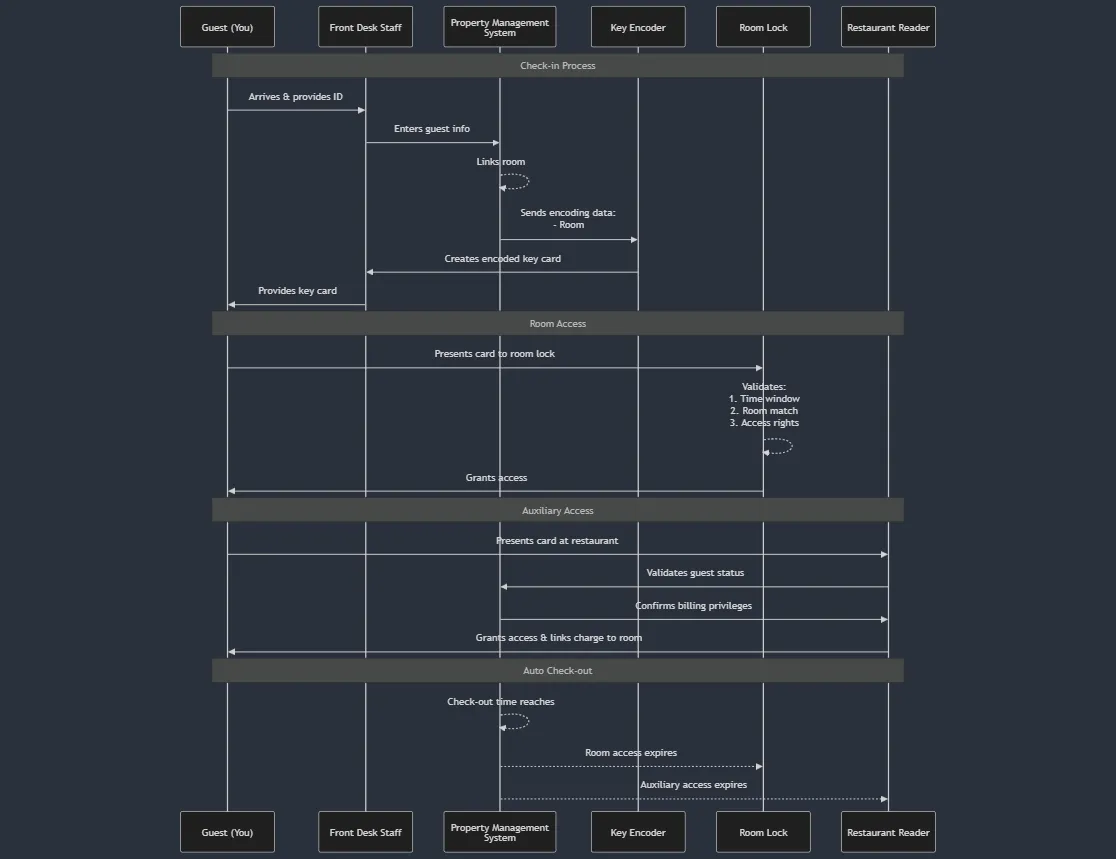
Here’s a high-level diagram of the general key card life cycle and use cases, as I saw them.
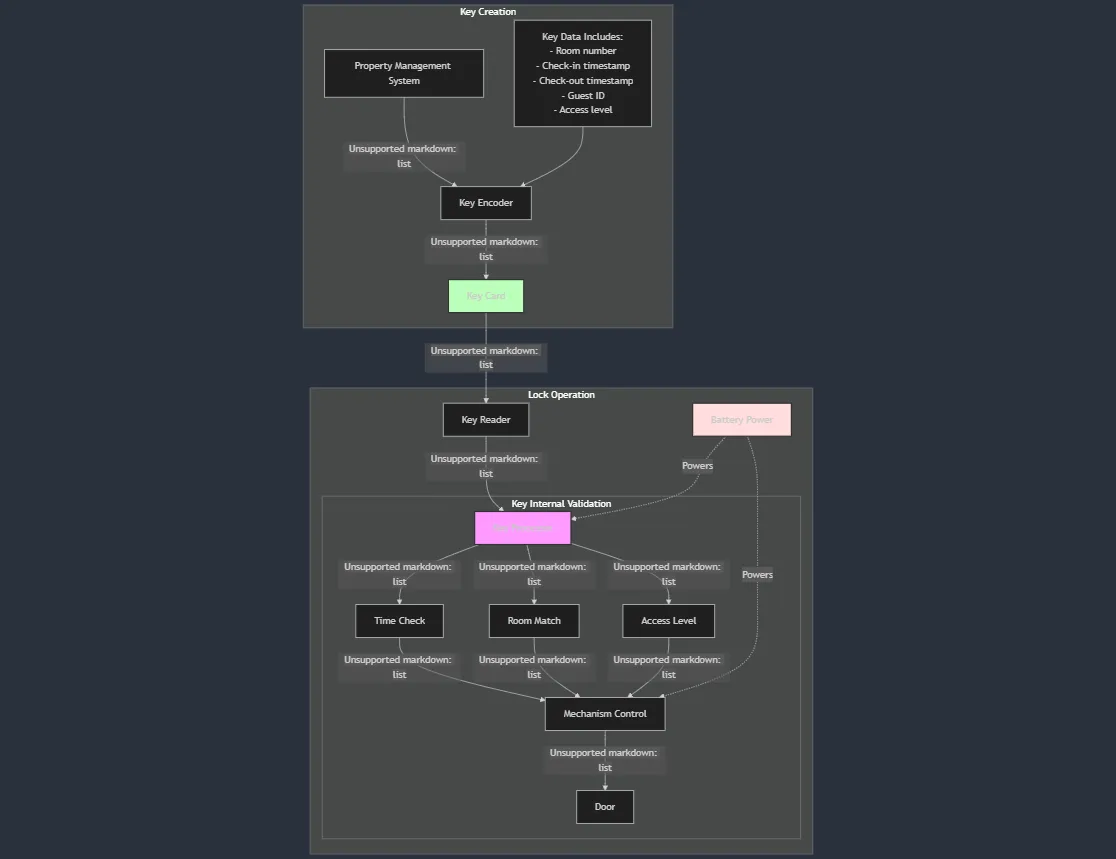
Key Card Creation Process
And here’s a more detailed breakdown of how I imagine the key card creation + usage going down.
Security Vulnerabilities
Physical Vulnerabilities
- RFID chips can be read and potentially cloned
- Depending on the frequency of the chip and whether or not it uses some sort of authentication protocol, that could vary in degree of ease, but it can be done.
- Key cards can be lost or stolen
- If our bad actor has some spy skills, encoding equipment could be physically accessed
Technical Vulnerabilities
The network communications between systems present another potential vulnerability. When a key card is encoded, sensitive data must flow between the PMS, the front desk computer, and the key encoder. If this traffic isn’t properly encrypted, a bad actor could potentially:
- Intercept the encoding instructions
- Capture the encryption keys or algorithms being used
- Monitor patterns in the data to identify weaknesses
Human Factor Vulnerabilities
- Front desk staff may issue replacement cards without proper verification
- I actually tested this one. No less than three times (from three different employees) I receieved a new key card for my room with no verification required outside of the room number.
- Guests may share access credentials
- Staff may not follow security protocols consistently
Potential Exploitations
Unauthorized Access
- Request someone else’s room key at the front desk
- Clone RFID data from exposed cards/bracelets
- Exploit weak encryption in the key writing process
- By taking an rfid chip (or several) to a secure location, a bad actor could analyze the encrypted values in an attempt to crack the hotel’s encryption algorithm. This one is probably a long shot, but the hotel might be using some low-entropy process or have a weak encryption key. Once the encryption algorithm is cracked, new key cards with varying access levels could be written.
Financial Fraud
- Charge purchases to other guests’ rooms
- Access billing information through system vulnerabilities
- The PMS system contains guests’ payment information, and may have it’s own vulnerabilities.
Data Theft
- Extract guest data from compromised key cards (if the encryption algorithm has been cracked)
- Intercept network traffic during key operations
Risk Mitigation
Hotel Remediations
MFA System Implementation
Benefits:
- Reduced risk of unauthorized access
- Better audit trail of key card requests
- Enhanced guest confidence in security
Costs:
- Increased complexity for front desk staff
- Potential guest friction during key replacement
- Training requirements for staff
Mobile Key System
Benefits:
- Elimination of physical key card vulnerabilities
- Modern guest experience
Costs:
- Significant initial infrastructure investment
- Guest adoption challenges (we all know who I’m talking about)
- Need for backup systems for phones without power
- Tech support nightmare (see ‘guest adoption challenges’)
Personal Safeguards
Physical Security
- Never leave your key card/bracelet unattended in public areas
- Use the manual deadbolt or security latch when in your room
- Store valuables in the room safe
Financial Protection
- Consider declining to link your key card to payment privileges
- If you do link payment, set up alerts for room charges
Access Control
- Report lost cards immediately to the front desk
- Request new cards if you suspect yours has been compromised
- Don’t share your room number or key card with others
Conclusion
For any hotels that can swing it, it’s best to just rip off the bandaid and move to mobile. For those that really can’t, maybe an MFA solution is a good compromise until mobile key cards become more accessible.
